Hybrid Deployment (The Transition Path)
Hybrid Architecture
Entra Hybrid Join & Coexistence With Entra Join
Best practice is Entra Hybrid Join for existing machines where we want to preserve user profiles. New machines get new profiles anyway so can start to employ Entra Join. Once all users have gone through their hardware refresh cycle, the company is 100% Entra Joined.
Windows Hello for Business GPO
Entra Hybrid Join is a prerequisite for WHfB in this deployment — the device must be domain-joined and Entra-registered before the Cloud Kerberos Trust can be established. Once Hybrid Join is complete, Windows Hello for Business deployed by GPO allows the background Intune enrollment process to meet the MFA requirements of an "all resources" MFA Conditional Access policy without prompting the user.
Intune Enrollment GPO
Hybrid Entra Joined machines are directed to enroll in Intune by an AD GPO (Entra Joined machines enroll in Intune directly).
Conditional Access for Hybrid Join
Since we are deploying Windows Hello for Business before Intune enrollment, we don't need to create an exception in our MFA Conditional Access policies for the Microsoft Intune Enrollment app.
Hybrid Deployment Checklist
Microsoft endpoint management tends to be asynchronous. Machine checks in, something happens, machine checks in again, the next step happens. This leads to latency in policy application. Two approaches to these latencies are illustrated below. I tend to be the guy on the left and want to see my changes right away. This deployment and troubleshooting is written from that perspective - providing the commands to push the process along. Once initial deployments are complete, a more relaxed approach can make sense.

Phase 1: Address Third Party Software
Third party encryption and antivirus can interfere with BitLocker and Defender for Endpoint.
- [ ] Third Party Encryption:
- Decrypt third party encrypted disks and uninstall third party encryption software.
- Otherwise, exclude this machine from BitLocker encryption to avoid double encryption.
- [ ] Third Party Antivirus:
- Uninstall third party antivirus software.
- Otherwise, Defender for Endpoint in passive mode can coexist with third party antivirus.
- Windows 10 & 11 (Automatic): Defender automatically flips to Passive Mode.
- Windows Server (Manual): Set registry to force Passive Mode before MDE onboarding.
- Path:
HKLM\SOFTWARE\Policies\Microsoft\Windows Advanced Threat Protection - Name:
ForceDefenderPassiveMode - Type:
REG_DWORD - Value:
1
- Path:
Phase 2: Create DNS Discovery Records
Before a device can enroll in Intune, it needs to know where to find your specific Intune cloud environment. It does this by asking the public internet for directions using your company's domain name (e.g., user@contoso.com).
You must create two CNAME (Canonical Name) records in the public (and private) DNS settings for your domain (usually managed wherever you bought your domain, like GoDaddy, Cloudflare, or Network Solutions).
You must create these two records for every email domain your users sign in with (e.g., if users sign in with @contoso.com and @contoso.net, you need to create these records on both domains).
First DNS Record: Entra Hybrid Join
Entra Hybrid Join requires the device to receive instructions from an authoritative source in Active Directory. This either takes the form of a Group Policy Object (GPO) or a Service Connection Point (SCP). This conveys the intention of a trusted admin to manage settings on this device.
| Host Name | enterpriseregistration.[yourdomain.com] |
|---|---|
| Record Type | CNAME |
| Value | enterpriseregistration.windows.net |
| Purpose | Tells the device where to register its identity in Entra ID. |
Second DNS Record: Intune Autoenrollment
If these CNAME records are missing, Phase 3 (joining the domain) might succeed, but Phase 5 (Intune Enrollment) will silently fail. The device will be joined to the network, but it will be "blind" to the Intune management servers.
- GCC High
- Commercial
| Host Name | enterpriseenrollment.[yourdomain.com] |
|---|---|
| Record Type | CNAME |
| Value | enterpriseenrollment-s.manage.microsoft.us |
| Purpose | Tells the device where the GCC High Intune enrollment server is located. |
| Host Name | enterpriseenrollment.[yourdomain.com] |
|---|---|
| Record Type | CNAME |
| Value | enterpriseenrollment-s.manage.microsoft.com |
| Purpose | Tells the device where the Commercial Intune enrollment server is located. |
Phase 3: Entra Hybrid Join
Entra Hybrid Join takes several steps and line-of-sight to a domain controller (may need VPN).
-
[ ] Entra Hybrid Join Targeted Deployment:
- GPOs allow you to create a targeted Entra Hybrid Join deployment.
gpupdate /forceto sync GPOs to this devicegpresult /r /scope computerto see what GPOs have been applied to this device- These are the registry keys applied by this GPO:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\CDJ\AAD\TenantIdHKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\CDJ\AAD\TenantName
-
[ ] Entra Connect:
- Entra Connect needs to be configured for Entra Hybrid Join.
- Synchronization Service Manager provides a real-time view of adds, updates, and deletes.
-
[ ] Entra Hybrid Join Process:
-
A: User sign-in triggers Automatic Device Join task.
Task Scheduler Library>Microsoft>Windows>Workplace Join- Right-click the task named Automatic-Device-Join and select Run.
- Alternatively, you can type
dsregcmd /join. - You can see the results in Event Viewer
Applications and Services Logs>Microsoft>Windows> User Device Registration > Admin- Event ID 304 ("The registration of the device was successful").
- Event ID 305 (Registration failed). ex:
0x801c001d(SCP missing)
-
B: Task queries AD for service connection point (or registry for our targeted deployment).
- CRITICAL: May fail if VPN/Line-of-Sight is missing.
- CRITICAL: Fails if device can't resolve
enterpriseregistration.windows.netvia public DNS.
# If using SCP (and not a targeted deployment) run this to see what your computers see in AD.$scp = Get-ADObject -Filter 'objectClass -eq "serviceConnectionPoint" -and name -eq "62a0ff2e-97b9-4513-943f-0d221bd30080"' -SearchBase (Get-ADRootDSE).configurationNamingContext -Properties keywords$scp.keywords -
C: Task creates a self-signed certificate and writes it to the computer object in AD.
-
D: Entra Connect detects and writes certificate to Azure DRS which (eventually) writes to Entra.
-
Synchronization Service Manager will display the computer object being sync'd to Entra.
-
The device will now show as "Pending" in the Entra Portal.
Devices Stuck In PendingThere is a common issue where an old "Entra Registered" (BYOD) record exists for the same machine. The duplicate record blocks the "Hybrid Joined" record from completing the handshake.
For a single wedged device — see the full clean-down and re-onboard procedure that preserves the user profile at Entra Device Hygiene § Single-Device Remediation. Quick fix from the local prompt: rundsregcmd /debug /leaveas SYSTEM to clear the local state, then delete the duplicate Entra record before retrying.
-
-
E: Task keeps retrying until step D is complete and Entra issues an ID token to the computer.
-
F&G: Task processes ID token and sends cert request to DRS which returns cert and updates Entra.
- The device status in the Entra Portal will now change from "Pending" to a joined date and time.
-
H: Device registration completed and task exits.
Once the background registration tasks finish, you must verify that the device has not only joined the directory but has also successfully "discovered" the Intune management endpoints.
-
Run the Verification Command: Open a Command Prompt and type:
dsregcmd /status -
Verify Identity & Auth State: In the Device State and User State sections, confirm the following:
AzureAdJoined : YES— The device has a unique identity in Entra ID.DomainJoined : YES— The device maintains its anchor to your local Active Directory.AzureAdPrt : YES— CRITICAL. This "Primary Refresh Token" is the secret sauce. Without aYEShere, the "Silent" Intune enrollment in Phase 5 will fail because the device cannot authenticate to the service without prompting the user.
-
Verify Discovery: Scroll down to the Tenant Details section. This is where you verify that the device "sees" your sovereign cloud tenant:
- GCC High
- Commercial
MdmUrl: Must point tohttps://enrollment.manage.microsoft.us/enrollmentserver/discovery.svcMdmTouUrl: Must point tohttps://portal.manage.microsoft.us/TermsofUse.aspx
Critical Sovereign CheckIf MdmUrl points to a .com address, the machine is attempting to enroll in Commercial.
MdmUrl: Must point tohttps://enrollment.manage.microsoft.com/enrollmentserver/discovery.svcMdmTouUrl: Must point tohttps://portal.manage.microsoft.com/TermsofUse.aspx
Critical Sovereign CheckIf MdmUrl points to a .us address, the machine is attempting to enroll in USGov.
-
Troubleshooting Discovery (The DNS Link):
-
If the MDM URLs are blank: The device identity is registered, but it is "blind" to the Intune service.
-
The Check: Verify your Public DNS (and Internal DNS if split-brain) contains the following CNAME record for every UPN suffix in use:
- GCC High
- Commercial
Host Name enterpriseenrollment.[yourdomain.com]Record Type CNAME Value enterpriseenrollment-s.manage.microsoft.usPurpose Tells the device where the GCC High Intune enrollment server is located. Host Name enterpriseenrollment.[yourdomain.com]Record Type CNAME Value enterpriseenrollment-s.manage.microsoft.comPurpose Tells the device where the Commercial Intune enrollment server is located. -
The Scope: Ensure the user's account is included in the MDM User Scope under Entra ID > Mobility (MDM and MAM) > Microsoft Intune.
-
-
Success Indicator (Entra Portal): In the Entra Admin Center, the device record should move from a "Pending" status to displaying a specific Join Type (Microsoft Entra hybrid joined) with a valid Registered date and time.
-
-
Phase 4: Windows Hello for Business
Unlike Entra Join, where enrollment is interactive, Intune enrollment for Hybrid Joined machines runs as a background, non-interactive task. It authenticates using the Primary Refresh Token (PRT) from the user's current Windows logon session. If that PRT carries no MFA claim — which is the case after a plain password login — the enrollment task fails silently with Event ID 76 (0x8018002A: MFA required).
WHfB at Windows logon is what mints a PRT carrying the phishing-resistant MFA claim the background task needs. It must be provisioned on this machine before Phase 5 triggers.
For GPO configuration steps (Cloud Kerberos Trust + WHfB GPO), diagnostic commands (dsregcmd /status Ngc fields, Event Viewer logs), and common silent blockers, see Windows Hello for Business Setup & Troubleshooting.
For the full set of phishing-resistant Windows logon options including PIV cards and FIDO2 NFC keys for environments where cameras, fingerprint readers, and USB ports are not viable, see Phishing-Resistant Authentication.
Phase 5: Intune Enrollment
Entra Hybrid Join and Windows Hello for Business prepares machines for Intune enrollment.
When you are in the "Frenzied Deployment" phase, waiting 2-24 hours for an Entra ID Dynamic Group to calculate membership is painful.
Best Practice: Target your policies to "All Devices" and use Intune Filters (e.g., device.model -startsWith "Surface") to include/exclude machines.
Why: Filters are evaluated by the Intune engine at check-in time (milliseconds), whereas Dynamic Groups rely on the background Entra ID sync cycle (hours).
-
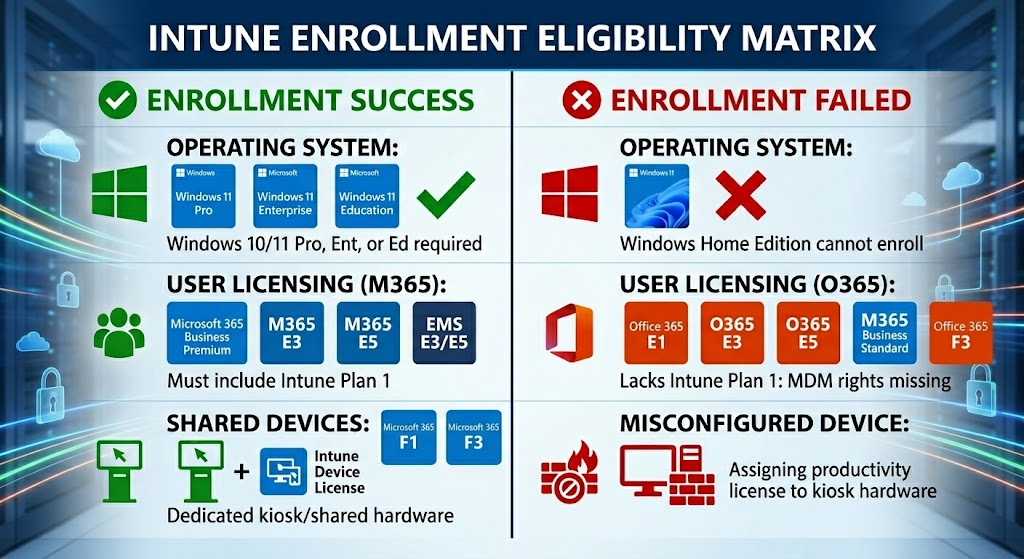
[ ] Verify Licensing:
- Does the user logging in have an Intune Plan 1 (or M365 G3/G5) license assigned active?
- Does the user logging in have an Intune Plan 1 (or M365 G3/G5) license assigned active?
-
[ ] Entra Configuration for Intune Enrollment — set MDM User Scope and WIP User Scope per Entra Join (The Cloud-Only Path) — Phase 2. The MDM scope and WIP=None trap apply identically to hybrid; the rest of this phase is what makes hybrid different.
-
Computer Configuration > Administrative Templates > Windows Components > MDM > Enable automatic MDM enrollment using default Microsoft Entra credentials- To verify GPO application: run
gpresult /r /scope computer.- Look for policy named as above.
-
[ ] Task Scheduler:
Microsoft > Windows > EnterpriseMgmtand find the MDM enrollment task- You can check last run result for any errors
-
[ ] Event Viewer Error Checking:
- Check Event Viewer:
Applications and Services Logs > Microsoft > Windows > DeviceManagement-Enterprise-Diagnostics-Provider > Admin. - Look for Event ID 76 indicating failure (Example: 0x8018002A due to missing MFA claim).
- Example Root Cause: Missing Primary Refresh Token (PRT).
- Example Fix: Ensure user has signed into Windows Hello for Business or a Microsoft 365 App (Teams/Outlook) to acquire a PRT.
- Check Event Viewer:
-
[ ] Manual Intune Enrollment
-
If the device shows as "Managed by MDE" in the portal, enrollment has failed.
-
Force Retry Command:
%windir%\system32\deviceenroller.exe /c /AutoEnrollMDM- Note: This command produces no output. Check Task Manager to see
deviceenroller.exerunning briefly, or refresh the Event Viewer log after 30 seconds.
- Note: This command produces no output. Check Task Manager to see
-
Force Policy Sync (UI Method):
- If the Info button is present (see above), click it.
- Scroll down to Device sync status.
- Click the Sync button.
- Why: This forces the device to reach out to Intune immediately for the latest policies, scripts, and app installs without waiting for the scheduled background cycle.
-
Success Indicators:
- Visual Verification (The "Info" Button)
- Open Settings > Accounts > Access work or school.
- Click the connected domain/account (e.g.,
connected to contoso.com). - Success: You see an Info button. This confirms the device is MDM enrolled.
- Failure: You only see a Disconnect button. This usually means the device is Entra Registered but not Intune Enrolled.
- Run
dsregcmd /status- User State
WamDefaultSet: YESWamDefaultAuthority: organizations
- User State
- Visual Verification (The "Info" Button)
-
Success: The device is Hybrid Joined, Intune enrolled, and operating under policy. At this point the device should appear as Compliant in the Intune portal (once compliance policies evaluate) and the user should be able to access cloud resources without additional MFA prompts after signing in with Windows Hello for Business.
-
📩 Don't Miss the Next Solution
Join the list to see the real-time solutions I'm delivering to my GCC High clients.